Over the last couple of years, I keep on coming across Zero-Trust Architecture (ZTA). A simple way to explain is that the standard model of security is known as perimeter security model, where everything within the perimeter can be trusted. In zero-trust (ZT) model, no assumptions is made about trustworthiness and hence it is also sometimes known as perimeterless security model.
This short video from IBM clearly explains what ZT means:
This blog post from Palo Alto Networks also clearly explains ZT:
By definition, Zero Trust is a strategic approach to cybersecurity that secures an organization by eliminating implicit trust and continuously validating every stage of a digital interaction. Zero Trust for 5G removes implicit trust regardless of what the situation is, who the user is, where the user is or what application they are trying to access.
The impact of Zero Trust on network security specifically protects the security of sensitive data and critical applications by leveraging network segmentation, preventing lateral movement, providing Layer 7 threat prevention and simplifying granular user-access controls. Where traditional security models operate under the assumption that everything inside an organization’s perimeter can be trusted, the Zero Trust model recognizes that trust is a vulnerability.
In short, Zero Trust for 5G presents an opportunity for service providers, enterprises and organizations to re-think how users, applications and infrastructure are secured in a way that is scalable and sustainable for modern cloud, SDN-based environments and open-sourced 5G networks. Delivering the Zero Trust Enterprise means taking Zero Trust principles, making them actionable and effectively rebuilding security to keep pace with digital transformation.
A research paper looking at Intelligent ZTA (i-ZTA) provides an interesting approach to security in 5G and beyond. The paper can be downloaded from here. The abstract states:
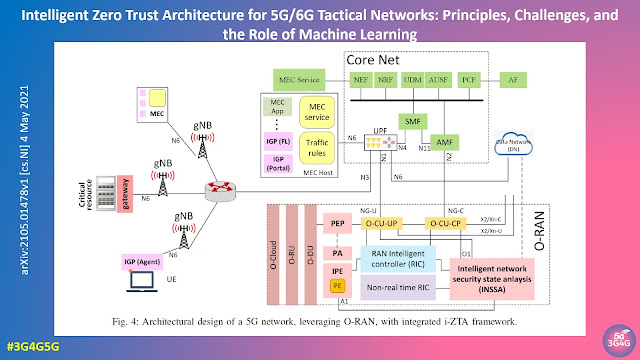
While network virtualization, software-defined networking (SDN), and service-based architectures (SBA) are key enablers of 5G networks, operating in an untrusted environment has also become a key feature of the networks. Further, seamless connectivity to a high volume of devices in multi-radio access technology (RAT) has broadened the attack surface on information infrastructure. Network assurance in a dynamic untrusted environment calls for revolutionary architectures beyond existing static security frameworks. This paper presents the architectural design of an i-ZTA upon which modern artificial intelligence (AI) algorithms can be developed to provide information security in untrusted networks. We introduce key ZT principles as real-time Monitoring of the security state of network assets, Evaluating the risk of individual access requests, and Deciding on access authorization using a dynamic trust algorithm, called MED components. The envisioned architecture adopts an SBA-based design, similar to the 3GPP specification of 5G networks, by leveraging the open radio access network (O-RAN) architecture with appropriate real-time engines and network interfaces for collecting necessary machine learning data. The i-ZTA is also expected to exploit the multi-access edge computing (MEC) technology of 5G as a key enabler of intelligent MED components for resource-constraint devices.
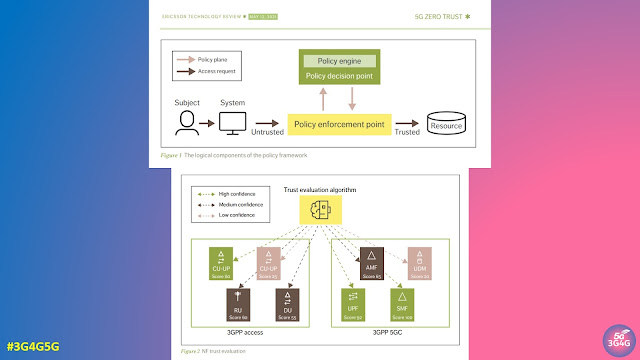
Ericsson Technology Review covered Zero Trust in 5G Networks in one of their issues. Quoting from the article:
The 3GPP 5G standards define relevant network security features supporting a zero trust approach in the three domains: network access security, network domain security and service-based architecture (SBA) domain security.
The network access security features provide users with secure access to services through the device (mobile phone or connected IoT device) and protect against attacks on the air interface between the device and the radio node. Network domain security includes features that enable nodes to securely exchange signaling data and user data, for example, between radio and core network functions (NFs).
The 5G SBA is built on web technology and web protocols to enable flexible and scalable deployments using virtualization and container technologies and cloud-based processing platforms. SBA domain security specifies the mechanism for secure communication between NFs within the serving network domain and with other network domains.
While the new requirements and functionality introduced in the 5G specifications are already aligned with many of the zero trust tenets. It is already evident, however, that further technology development, standardization and implementation are needed in areas such as policy frameworks, security monitoring and trust evaluation to support the adoption of zero trust architecture in new telecom environments that are distributed, open, multi-vendor and/or virtualized.
While various technologies can support organizations in adhering to the guiding principles of zero trust as part of their total active defense strategy, it is important to remember that technology alone will never be sufficient to realize the full potential of zero trust. Successful implementation of a network based on zero trust principles requires the concurrent implementation of information security processes, policies and best practices, as well as the presence of knowledgeable security staff. Regardless of where a CSP is in its transition toward a zero trust architecture, the three pillars of people, processes and technology will continue to be the foundation of a robust security architecture.
Related Posts:
- 3G4G: 5G Security Overview by Mpirical
- The 3G4G Blog: Key Technology Aspects of 5G Security by Rohde & Schwarz
- The 3G4G Blog: Bug hunting in 5G Networks and Devices
- The 3G4G Blog: Impact of 5G on Lawful Interception and Law Enforcement.
- The 3G4G Blog: AT&T Cybersecurity Experts Provide 5G Security Overview
- The 3G4G Blog: Everything you need to know about 5G Security
- The 3G4G Blog: Nokia Lectures in Collaboration with Bangalore University
- The 3G4G Blog: Lawful Intercept in 5G Networks
- The 3G4G Blog: 5G Roaming with SEPP (Security Edge Protection Proxy)
No comments:
Post a Comment