Cross posting from LinkedIn, please post any comments there!
One of the advantages of having been in the industry for a very long time is one knows (and in my case, remembers) the hacks of each generation of mobile technology.
In case of UMTS (3G), the initial version had very poor data rates. Even though 3G was designed to bring data to the masses, there were hardly any applications that could take advantage of the mobile data connectivity. In addition, you could hardly get over 128 kbps (yes, kilo bits per second, not mega bits).
Most people think that the data part was added later on, as HSDPA, HSUPA (collectively HSPA) and HSPA+ from 3GPP Release-5 onwards. This is just one side of the story. The initial version of 3G had Downlink Shared Channel (DSCH) and Uplink Common Packet Channel (CPCH). As nearly all the patents were held by one very small company, none of the big vendors (both in network side as well and device side) implemented it (cartel?) and those channels eventually got removed from the standards.
Politics aside, until the arrival of HSPA, people couldn’t take advantage of mobile broadband.
LTE had already started being standardised while HSPA was being rolled out. LTE promised much higher data rates and reduction in the device power consumption, and it delivered! But…
Have you heard this industry joke? When the standards engineers were designing 3G, 2G voice and SMS was generating most of income for the operators. Naturally they focussed on Voice and SMS and forgot to design data properly. When it came to design LTE, they focussed so much on data, they forgot to design the voice part.
Not My Job
Well, to be honest, 4G was always planned to be a packet switched (PS) only network, with a flatter and simplified architecture and protocols. With CS domain gone, the RRC and NAS protocols could be simplified. From a RAN engineer point of view, the voice calls would be voice over IP (VoIP) but the people who design the network telephony part didn’t get the memo.
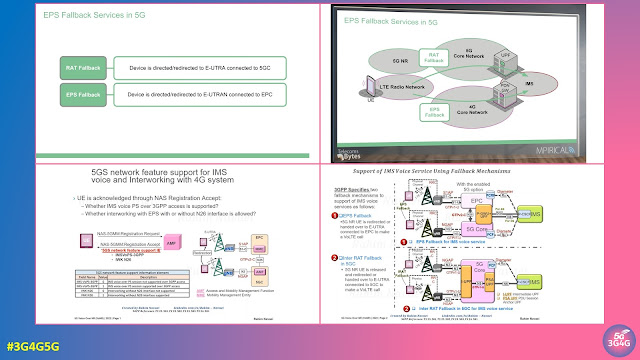
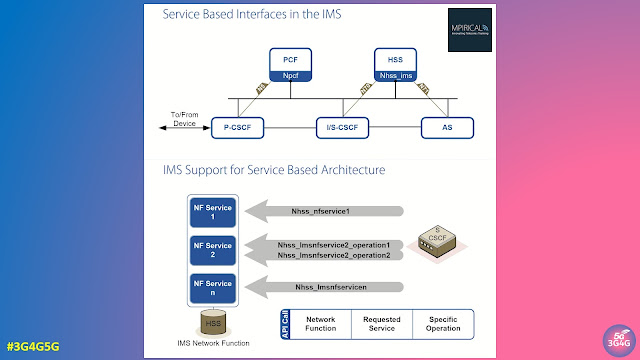
The first set of LTE standards in Release-8 had to rely on this hack called CS Fallback. When nobody was taking ownership of the issue on hand, GSMA stepped in and created Voice over LTE (VoLTE) standards. It was based on the IMS standards that were bandied about for a long time but never got deployed fully. The standards was also complex and even after 8 years of it being standardised, it has still not been deployed everywhere.
5G for Everyone
I have been closely following the developments in 5G for over 6 years now. If you saw and heard the things I did, you would have believed that 5G is a panacea for all the world’s ills. In fact, in reality, it is just another generation of mobile network standards, astutely referred to as 5G JAG (Just Another Generation) by the outspoken industry analyst, Dean Bubley.
In the race to launch 5G by hook or by crook, the Non-Standalone (NSA) version of 5G, option 3 (technical name EN-DC) was launched. It gives the operators the ability to show 5G icon on you smartphones easily while not having to worry too much about delivering all the promises. If an operator has spare or a lot of spectrum, they can then use (some of) it to start transmitting on 5G New Radio (NR). If they don’t have much spectrum then they will have to do some kind of Dynamic Spectrum Sharing (DSS) to show the 5G icon. The problem with DSS is that while it would provide some kind of 5G to everyone capable of receiving it, it spoils the experience of the 4G users who are satisfied or happy with their LTE network.
5G Stands Alone
While all this had been going on, the operators have started buying new 5G spectrum, and started preparing and in many cases rolling out the Real Standalone 5G Network. If an operator has sufficient spectrum and the right kind of spectrum, they can now start to deliver on some of the actual 5G promises.
I am aware of some of the operators who are already thinking about switching off their Non-Standalone EN-DC networks within the next couple of years. The initial 5G smartphones did not support the Standalone version of 5G networks so the operators will give them enough time to switch over to a newer device capable of standalone network.
So what would happen to a 5G device only supporting NSA 5G, after the NSA network is switched off?
Nothing really. It would still be able to do 4G (and 2G, 3G) which is generally good enough. They would stop seeing the 5G icon and in some cases, won’t benefit with the extra speeds boost.
Switching off 5G NSA will benefit the operator with the simplification of the network, not just from deployment point of view but also from optimization as there is no need for 4G-5G dual connectivity and for the 5G cell to be planned based on the 4G cell.
Industry’s View
5G Training ran a poll on LinkedIn to ask people involved in the 5G industry if they were happy with 5G NSA or would rather go with Standalone 5G, 6G or just satisfied with 4G. Surprisingly most people in the 5G industry said they were waiting for Standalone 5G. This was followed by “Looking forward to 6G!”. “Happy with existing 5G” got the least number of votes.
This poll is by no measure reliable but it should force the operators, vendors and everyone else to ponder if it makes sense to move to SA sooner rather than later and to switch off NSA as soon as possible.
Non-Standalone Part 2
When the first set of 5G standards were being defined, it was felt that there should be a path to transition from 4G to 5G in the future. While the initial Option 3 (EN-DC) relied on 4G Core or EPC, these future NSA options can rely on 5G core.
Sometimes, in their zeal and enthusiasm, engineers define things that would make everyone’s lives difficult. These options are very much like that. While some operators have asked for Option 4, most people realise that it doesn’t make sense, at least right now to be creating more fragmentation in 5G deployment.
Hopefully rationality will prevail and any major architecture changes we do with 5G going forward will only be done after lots of analysing and thinking about the long term consequences.
Please post any comments on LinkedIn as comments have been disabled on this post.